Here’s how you can use Microsoft Purview’s Data Loss Prevention (DLP) policies to safeguard your information from unauthorised access today.
Important:
As a best practice, always conduct a business impact assessment first. Doing activities 1 and 2 can disrupt legitimate business operations. Ask yourself:
- Do we have suppliers, partners, or customers in these regions?
- Are there ongoing projects requiring data exchange that will go to this region?
- Could this affect our global workforce or remote employees?
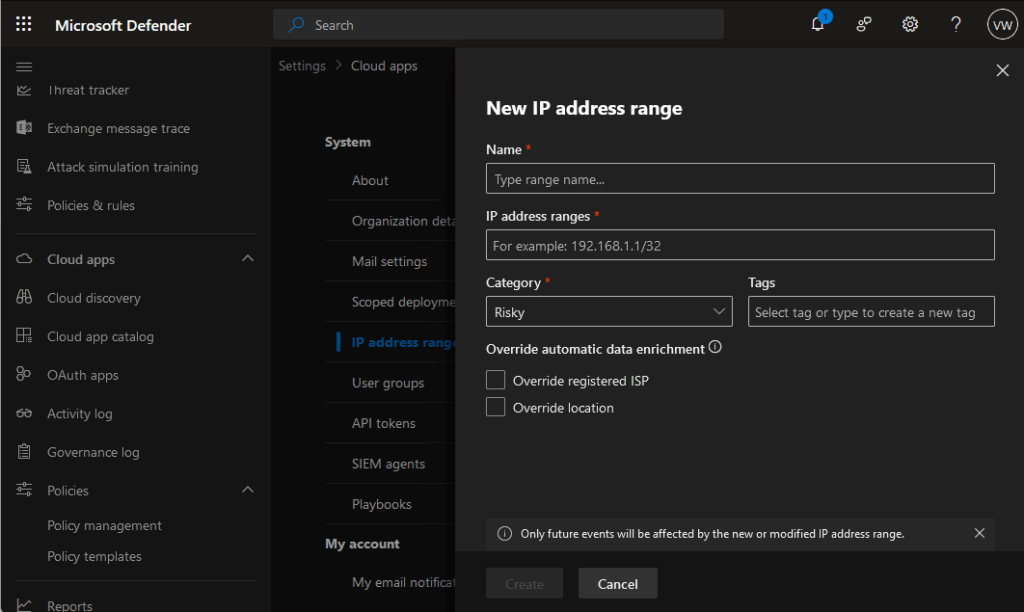
1. Block Risky IP Addresses
Start by implementing IP-based restrictions in your DLP policies. Block known IP addresses from high-risk countries to prevent data exfiltration attempts. This creates your first line of defence against unauthorised access from these regions.
You can do this through Defender for Cloud apps: https://learn.microsoft.com/en-us/defender-cloud-apps/ip-tags
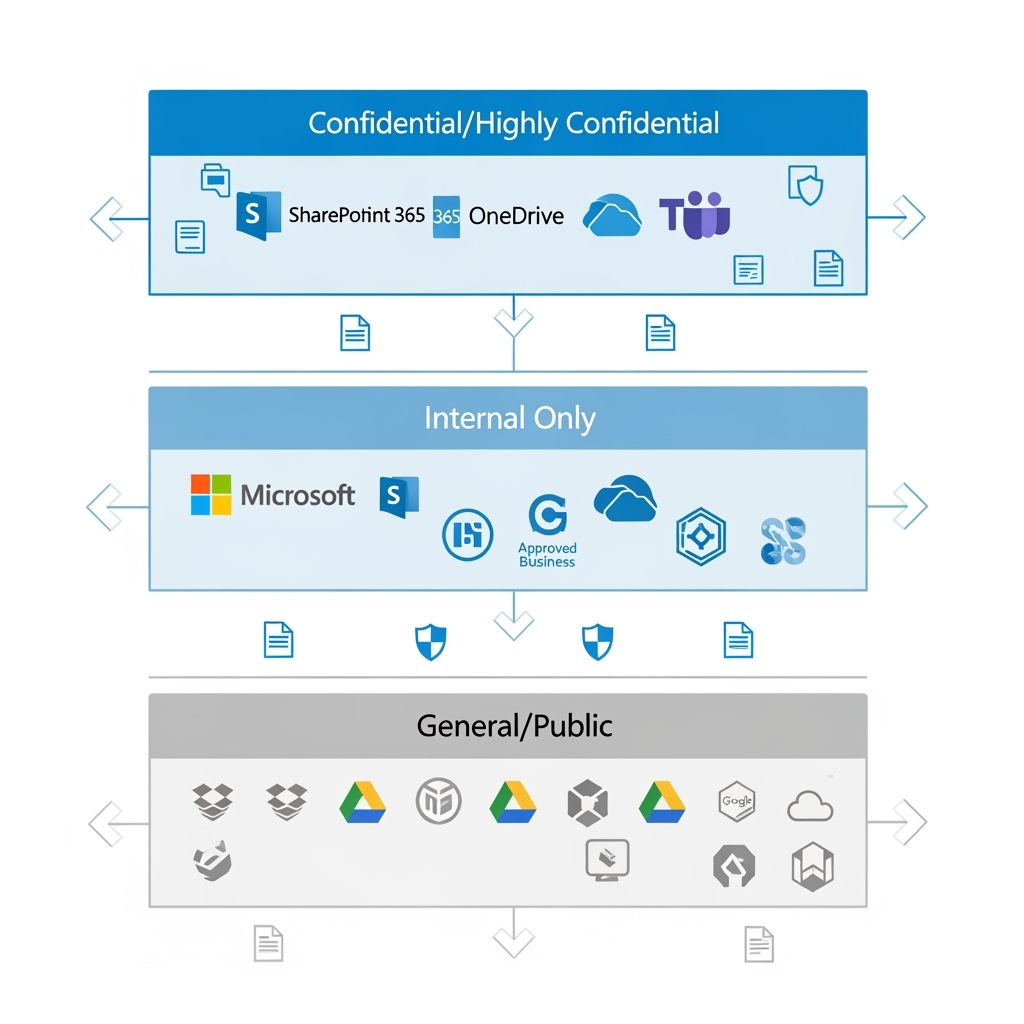
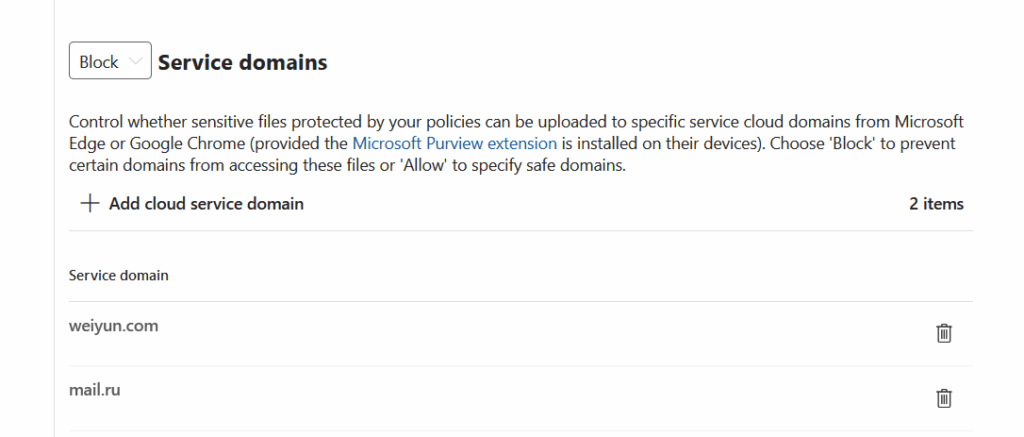
2. Restrict File Sharing to Risky Platforms
Many data breaches happen through seemingly innocent file sharing. Block access to popular file-sharing services hosted in these regions:
Here’s a few popular mail and file sharing sites for the 2 countries mentioned in the Microsoft Security Program post.
Russian platforms:
• Yandex.Disk (https://360.yandex.com/disk/)
• Mail.ru Cloud (https://mail.ru/)
Chinese platforms:
• Baidu Pan (https://pan.baidu.com/)
• Tencent Weiyun (https://www.weiyun.com/)
Configure your DLP policies to detect and block uploads to these services automatically.
You can also create a policy to block uploads to a group of domains, so that end-user will NOT be able to uploaded sensitive data through their devices. The can be configured for Purview Endpoint DLP.
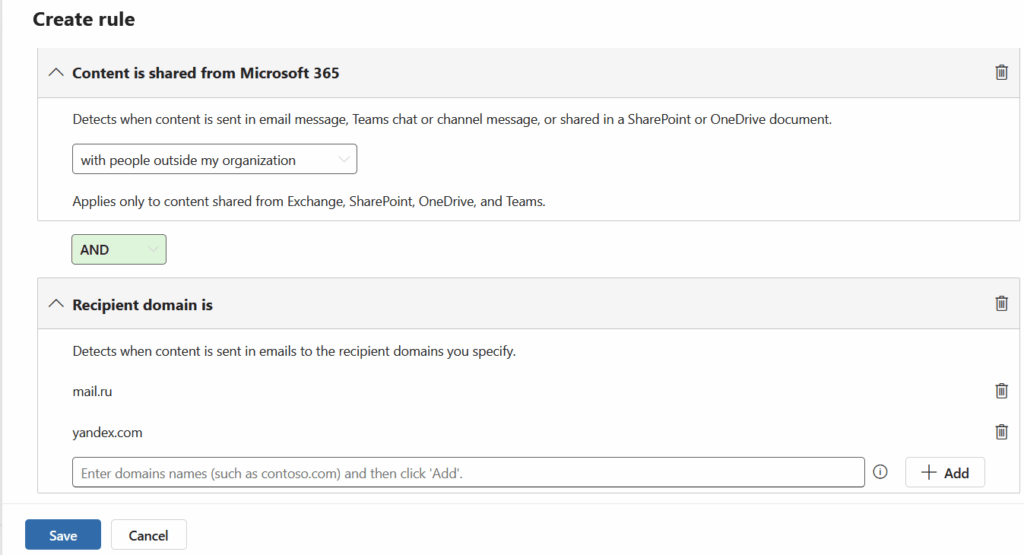
3. Monitor Email Communications
Email remains a primary vector for data theft. Block or monitor communications with popular email services from these regions, including Yandex.Mail, Mail.ru, QQ Mail, and 163.com. Your DLP policies can flag or prevent sensitive data from being sent to these domains.
4. Track Your Data’s Journey
Use Purview Information Protection’s Track and Trace feature to maintain visibility over your sensitive documents. This powerful tool shows you:
• Who’s accessing your protected files
• Where they’re being opened
• When access attempts occur
It’s like having a GPS tracker for your most valuable data.
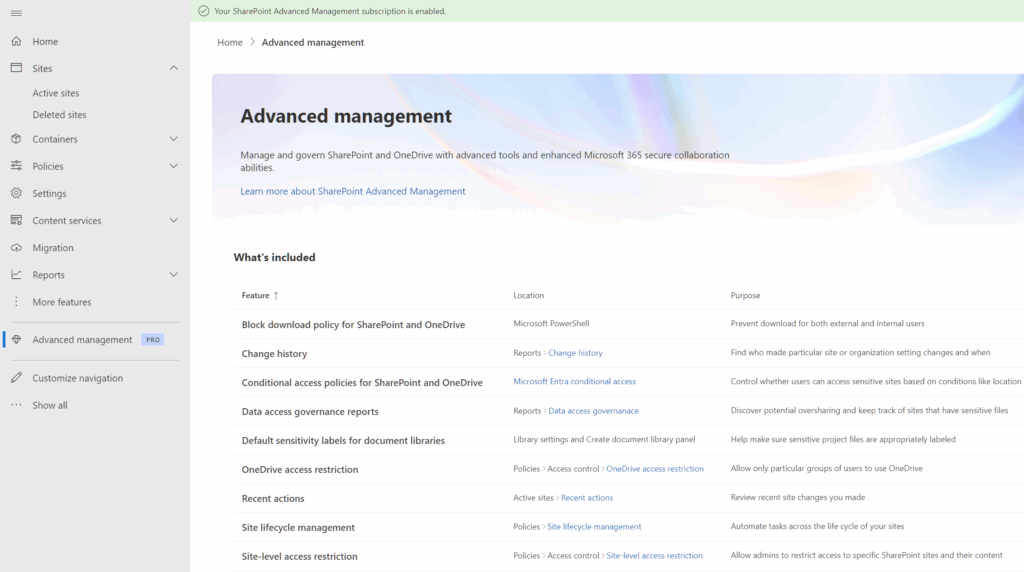
5. Regular Health Checks with SharePoint Advanced Management
Don’t set and forget. Use SharePoint Advanced Management to regularly review:
• Which files are being shared externally
• Who has access to sensitive documents
• Unusual sharing patterns that might indicate compromise.
Think of it as your monthly data health check-up.
Read up on how SharePoint Advance management works here: https://learn.microsoft.com/en-us/sharepoint/advanced-management
Additional tips:
Tip 1 : Start with monitoring and alerting rather than outright blocking. This lets you understand your data flows before implementing restrictions. You can always tighten controls once you’ve mapped legitimate business needs.
Tip 2: Consider creating exceptions for specific, verified business partners rather than blanket country blocks. This gives you granular control whilst maintaining necessary business relationships.
Remember, technology is only as strong as the people using it. Train your team to recognise suspicious requests and understand why these protections matter.