There are many, many post talking about Insider Risk Management but very little that talks about the practical, realistic and field tested approach to Insider Risk Management. This is my attempt to tip the scale towards the latter. I’m skipping the textbook definitions to share real-world scenarios from the trenches specifically, the messy, human problems clients have thrown at me and the practical, field-tested responses we’ve workshopped to address them.
Let’s start with the Human and the strategic foundations of Insider Risk which is…
The Human Element
Let’s be honest: we’ve built digital fortresses with firewalls taller than the Shard and MFA that demands a blood sample. But what happens when the threat isn’t a hooded hacker, but friendly Dave from Sales “backing up” his client list before jumping ship?
In the UK, 90% of organisations face insider incidents annually, and 74% are negligent. People like Dave who aren’t villains, just human [Source: Cybersecurity Insiders]. IRM isn’t about building higher walls; it’s about understanding who’s walking through the gate. With the FCA and GDPR watching closely, “set and forget” security will no longer work.
IRM is a Team Sport
If you think IRM is just a “Cyber Security thing,” you’re in for a rude awakening. It’s more like a heist movie, but instead of stealing diamonds, you’re trying to stop data from walking out the door. And you can’t do it alone. You need a “Triad of Trust” (there’s 4 below since I’ve not used Triad before):
- HR: They’re the ones who know Dave is leaving. They provide the context—resignations, performance reviews, the “vibes.” Without HR, you’re just watching random data movements and guessing.
- Legal: They’re the ones who keep you out of court. They ensure your monitoring doesn’t cross the line into “Big Brother” territory, keeping you compliant with employment law, Privacy laws and GDPR.
- IT/Cyber: You. The tech wizards. You provide the tools (Purview, DLP, Logging) and the forensic skills to figure out what’s actually happening.
- Business Leaders: They define what “sensitive” actually means. From M&A docs, merger docs; to Customer Support, it’s the client list. One size does not fit all.
Pro Tip: Form a small, cross-functional steering group. Call it the “Data Defence League” if you want. Just get them in a room.
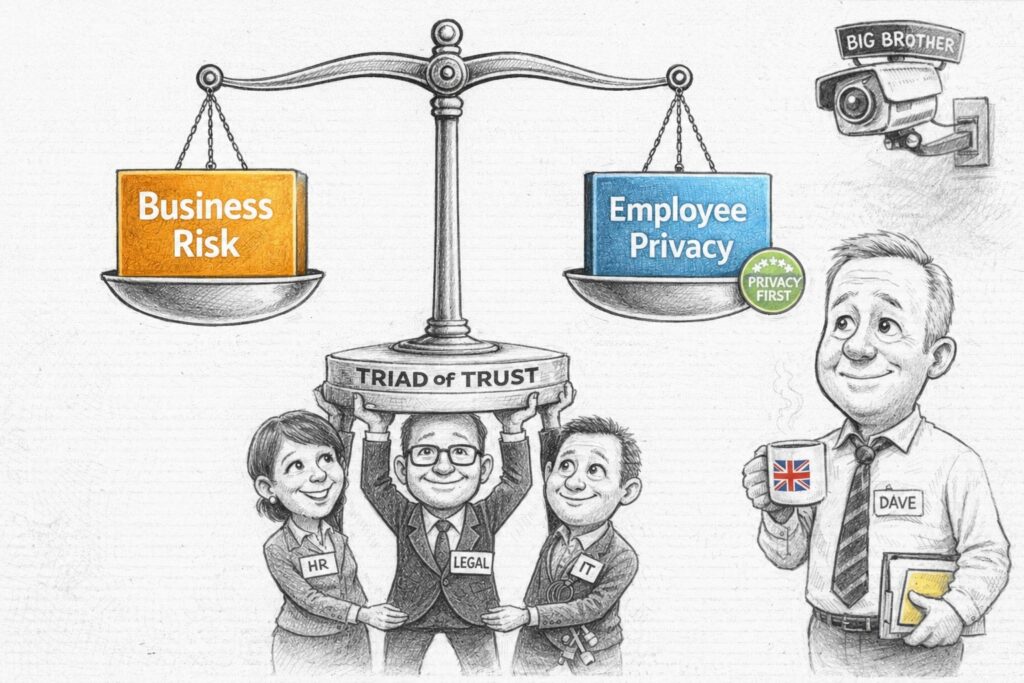
The Privacy Paradox (aka Balancing Monitoring with Trust)
Let’s address the elephant in the room: IRM tools are intrusive by design. They’re supposed to be. They monitor user activity and correlate events to spot patterns. But in the UK, we have a thing called “privacy,” and it’s kind of a big deal. Here’s how you can balance it.
The UK – GDPR Balance:
- Transparency: Tell people you’re watching. Update those employment contracts. Add it to your Employee Training program, include it your End-user Agreement that they see when they log-in to their Corporate PC. Send an email. Be open. Why: Because secrecy breeds mistrust.
- Proportionality: Don’t monitor the intern with the same intensity as the Head of M&A. Start with high-risk roles (Tier 1) and expand based on evidence. It’s called “being reasonable.”
- Pseudonymisation: This is your best friend. Purview keeps data private by default. Analysts see “ANON2340,” not “Dave from HR,” until a formal case is opened. It’s like a mask for your data.
- Policy-Led Monitoring: Only trigger monitoring when a highly defined policy is breached. This isn’t about general surveillance; it’s about catching specific, pre-agreed risk behaviors. If the policy isn’t broken, the system stays quiet.
You can’t protect what you haven’t classified
Here’s another hard truth. Purview IRM is only as good as the data it can see. If you haven’t done the boring work of classification, you’re flying blind. There’s a clear dependency chain:
- Sensitivity Labels: The bedrock. If a document isn’t labelled “Confidential,” IRM can’t prioritise it. It’s like trying to find a needle in a haystack without knowing what a needle looks like.
- Sensitive Information Types (SITs): Teach Purview to recognise UK-specific data like NINs, IBANs, or NHS numbers. If it doesn’t know what a NIN is, it can’t protect it.
- Data Loss Prevention (DLP): DLP is the “first line of defence.” IRM is the “second line” that investigates when DLP is bypassed or when subtle patterns emerge. Think of DLP as the bouncer and IRM as the detective.
Warning: If your DLP policies are noisy or your labels are inconsistent, your IRM alerts will be useless. Start by tuning your DLP and Classification strategy before turning on IRM. Otherwise, you’ll just be drowning in false positives.
Questions from my clients HR, Legal and Business Operations team
Q1 (HR/Legal): “How do we ensure we aren’t creating a ‘Big Brother’ culture that destroys employee morale?”
Answer: Focus on “Privacy by Design.” Use pseudonymisation, limit access to investigation data to a need-to-know basis, and ensure all monitoring is tied to a legitimate business interest (e.g., protecting IP) rather than general performance monitoring. Transparency is your best defence against mistrust. Think of it as “security with respect.”
Q2 (Business Ops): “How do we distinguish between ‘normal’ high-volume work and ‘risky’ data exfiltration, especially in data-heavy roles like Legal or Finance?”
Answer: Use “Scoped Policies” and “Baseline Behaviour.” Purview allows you to set different thresholds for different groups. A Legal team downloading 500 files for a DSAR is normal; a Sales rep doing the same is a risk. Use group-based scoping to reduce false positives and respect business context. It’s about context, not just volume.
Q3 (Legal/Compliance): “What are the legal repercussions for a first-time offender versus a repeat offender?”
Answer: Define a “Graduated Response” framework. First-time negligent offenses should trigger coaching and re-training. Repeat offenses or malicious intent should trigger formal HR/Legal escalation. Consistency is key to procedural fairness. Don’t fire Dave for a first-time mistake; teach him.
Q4 (IT/Security): “How do we handle long notice periods (e.g., 3-6 months) for senior leavers?”
Answer: Map AD “accountExpires” attributes to IRM triggering events. Configure a 90-day pre-expiry monitoring window to catch pre-resignation data gathering. It’s like having a security camera on the exit door.
Q5 (HR): “How do we integrate IRM with our existing HR processes for terminations?”
Answer: Use HR connectors to automatically flag resignations or terminations. This ensures IRM policies are triggered without manual intervention, reducing the risk of human error. Automate the boring stuff.
Q6 (Business Leaders): “How do we measure the success of our IRM programme?”
Answer: Track metrics like “Mean Time to Investigate,” “False Positive Rate,” and “Number of High-Severity Cases Resolved.” The goal is to move from reaction to resilience. Show them the value, not just the alerts.
